INTRODUCTION
This report will be integrating foreign intelligence (“FI”), covert action (“CA”) and competitive intelligence (“CI”) techniques to assist Carlyle Mobile Tech Inc. (“CMTI”) (a fictitious telecommunications company) enter the Indian telecommunications market. To achieve this, the report will examine how an assessment of the corporate environment in India will allow for intelligence techniques and insights to be effective in CMTI’s decision making capabilities. The report will assess the counterintelligence threats and the potential commercial espionage CMTI could face in India, it will also explore how CA principles can be executed in the area of marketing and advertising.
The body of the report will be broken down into five sections, with each section examining a segment of the market entry strategy using the appropriate intelligence discipline necessary to achieve the requisite outcome. Section one will examine why/if India is a viable target market and attempt to answer whether that market will be economically beneficial to CMTI, the initial stage of any viably foreign market entry is open source research; thusly open source intelligence (“OSINT”) will be used to gather the necessary information in the marketplace.
Section two will be used to determine CMTI’s objectives and goals in India. Answering two questions: “how can CMTI provide a better product?” and, “how can CMTI maintain their awareness the competitions offerings and posture?”. Therefore competitive intelligence is part of this section. Section three will use human intelligence (“HUMINT”), signals intelligence (“SIGINT”) and geographic intelligence (“GEOINT”) to select business partners in India and work with them over the long term through asset validation.
Section four will look at how to design an international marketing plan with the assistance of the psychological operations (“PSYOPS”) planning cycle and through the use of propaganda.
Finally, section five will examine how CMTI can keep their trade secrets and proprietary business plans secure, and out of the hands of competitors. This report constitutes a market entry plan for CMTI and will endeavor to make determinations as to the correct path for CMTI.
1. CHOOSING A TARGET MARKET
Before CMTI even considers entering a foreign marketplace, the most important concern is to identify whether the product it offers, in this case the CMTI Smartphone is appropriate for the global market place.[i] CMTI found success in the United States by introducing the $160 CMTI-S back in 2011. The product offers touchscreen, high-quality camera, access to emails, web browsing and the ability to download music, apps and games; increasing mobile accessibility to 18 – 35 year old urban consumers who are interested in high functioning devices for a reasonable price.[ii]
Due to CMTI’s limited product line the company has identified the CMTI Smartphone as its target product. CMTI believes that their smartphone can provide a comparable service to foreign consumers matching their domestic user profiles/demographics. CMTI is a company without prior international experience and will therefore be a first-time entry company. Thusly, to begin identifying an appropriate foreign market CMTI must acquire adequate and reliable FI in order to formulate to best possible decisions. The question becomes how is that FI acquired? The answer is OSINT.
“Today, open source … has become indispensable to the production of authoritative analysis” – John Gannon, retired CIA and former Chairman of the National Intelligence Council [iii]
Entry into a new and unfamiliar market, without reliable intelligence, will expose CMTI to unforeseen risks and could end the company’s foreign expansion before it even begins.[iv] To avoid that catastrophe, CMTI must use OSINT to effectively analyze the global telecommunications market to pinpoint the most appropriate market for entry. According to some sources, open source data may account for up to 80% of information used by the intelligence community.[v] This implies that OSINT is a central tool for gaining reliable and actionable FI and as such, it behooves CMTI to mount an effective OSINT effort; because no market entry strategy can be viable without it.
The use of OSINT would be to identify three things: a workable consumer profile, market size, and the potential for growth. Open source research into the global telecommunications industry would indicate to CMTI that the industry was growing at 5.3% annually reaching an estimated $2.7 trillion in 2017, with Asia expecting to grow at 64%, making the region a key market particularly for the CMTI Smartphone.[vi] Of those Asian markets, India has one of the fastest growing telecommunications industries.[vii]
Publically available information indicated that the Indian telecommunications industry increased their overall telephone subscribers from 1,002 million to 1,006 million between May and June 2015, showing a monthly growth rate of 0.49%.[viii] Between 2006 and 2013 the wireless and wireline components of the industry increased their combined revenue to over $39 billion, with large urban centers increasing their mobile usage.[ix] An ideal customer profile for the CMTI Smartphone may be an urban, rather than rural, mobile phone user in need of inexpensive high functional devices.
In addition to the above data, there are other reasons that make India an attractive market for CMTI. The country encourages an open and competitive market environment for both foreign and domestic companies; the regulatory framework within the country promotes a business friendly environment, providing an even playing field for foreign and domestic firms alike, a fact that CMTI can take advantage of; the judicial system is based on the British model and is highly developed and sophisticated; English is the language of business and government making access easier for companies like CMTI; and, the indigenous workers are highly skilled and offer competitive rates for their skills and services.[x]
India provides a marketplace with steady monthly growth, a stable business/governance environment and relatively easy access to an open and competitive industry. A prudent entry strategy into India can potentially see CMTI expand beyond the United States and increase revenues through investment into that country.[xi] With the target country identified, CMTI must now consider what the competitive environment is like.
2. DETERMINING GOALS AND OBJECTIVES
Targeting India for entry was a first step in this process. CMTI must now look to what they determine to be their objectives and goals within the Indian telecommunications market. Central to this, is gaining an awareness of their competition and what they offer the market. Therefore, to have a chance of success in India, CMTI must anticipate the activities of their potential rivals and develop a plan to effectively compete against them. To do this, they must incorporate competitive intelligence into their strategic planning. Competitive intelligence is the process of collecting and analyzing data related to their competitors, which allows a company such as CMTI to gain an advantage over their rivals.[xii] CMTI will use the cycle in the below figure.[xiii]
Figure 1.
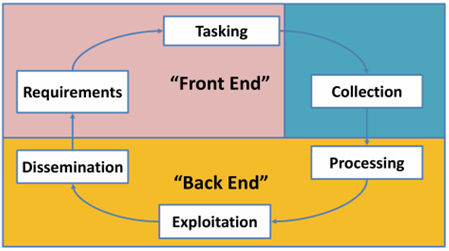
Source: Clark, R. “Perspectives on Intelligence Collection” (2013)
By implementing a competitive intelligence cycle based on the above diagram, CMTI will be able to understand the current and future strategies of their competitors. Particularly, in the case of the telecommunications industry, where specifics about technologies and products that may have an impact on the market in India.[xiv] Focusing in on the mobile phone market within the telecommunications industry, CMTI would realize that the market is highly competitive.[xv]
The smartphone segment within which the CMTI Smartphone will have to compete, is dominated by Samsung, Micromax, Nokia, Karbonn and Lava.[xvi] These participants have offered a variety of models for their smartphone offerings and have been offering their customers higher technologically capable products at lower costs.[xvii] The domestic firms have been offering devices in the $65 – $160 range while Samsung, Nokia, and other foreign brands have offered devices in the $160 – $650 range; more than double the price of the domestic companies.[xviii] As a result, the domestic players have been gaining market share against their foreign competitors;[xix] with Samsung’s share declining from 20.3% to 16.5% in late 2014.[xx]
What this tells CMTI is that the trend in the Indian market is for highly functional devices that are marked at a reasonable price. Like CMTI’s consumers in the United States, the Indian consumers are focused on excellent specs that is within their budgets.[xxi] Through this analysis of the market, using competitive intelligence, CMTI is able to position itself as an inexpensive alternative to Samsung and Nokia whilst competing directly with the domestic companies on price; who may be unable to compete technologically.
Additionally, the competitive intensity within the market will cause higher priced devices offered by other foreign competitors to become less viable, as prices continue to fall even as there is room for the market to grow.[xxii] The introduction of the CMTI Smartphone will help meet the demand for higher spec and smartphone devices. Also, these companies are underrepresented in the rural regions of the country. “Teledesity,” or the penetration of telecommunications services, is low in the rural areas in the country and CMTI may be able to target these regions in the country to create a consumer base that current market participants are under serving.
This analysis offers a snapshot of the current competitive environment, however, competitive intelligence also involves continual monitoring and developing an understanding of competitor strategies. CMTI must have a continual external focus on competitors, the market environment, products/prices and technological developments.[xxiii] Continual focus outward will allow CMTI to implement suitable strategies. Focusing on competitors’ moves and counter moves will increase CMTI’s own competitiveness.
Thusly, the objectives and goals that CMTI ought to focus on are to meet the needs of the Indian consumer, which are high specification devices at a reasonable cost. This will place them at a price advantage vis-à-vis Samsung and other foreign competitors and offer better technology than domestic competitors in India.
3. CHOOSING APPROPRIATE ENTRY MODE
Once CMTI has developed a market entry process targeted at India based on a foundation of research into the competitive environment of the Indian telecommunication industry, the company then needs to figure out the most appropriate entry mode.[xxiv] This section will assess the merits and weaknesses of the entry modes CMTI will need to consider. Before this exploration, it is important to understand what a foreign market entry mode constitutes.
Foreign market entry modes are established procedures that enable companies to introduce their skills, products, technologies and other offerings into a foreign country.[xxv] The selection of an appropriate entry mode is based on the size of the market (India being the second largest in the world for mobile devices), the competitive environment (highly competitive) and the product-market fit.[xxvi]
These entry modes are clustered into three classifications: (1) export entry modes, (2) contractual entry modes, and (3) investment entry modes, each of these steps would gradually increases CMTI’s exposure to India and as such enhances the risk profile of market entry.[xxvii] The following figure displays the advantages and disadvantages of each entry mode.
Figure 2.
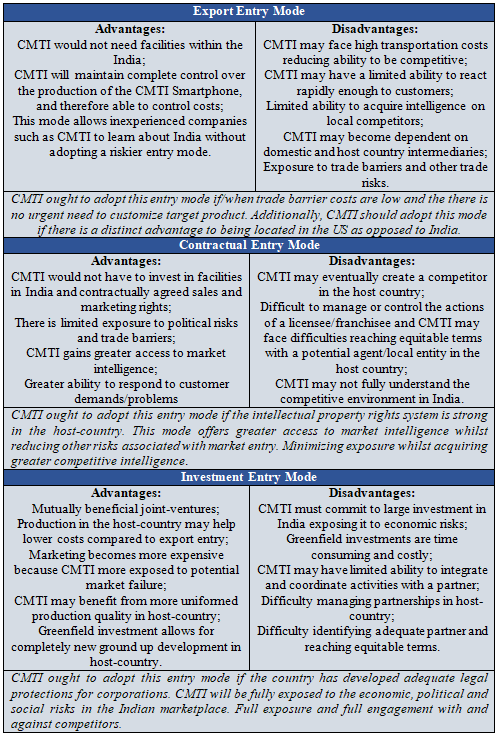
Source: Modified from Johnson, Gerry et al., “Exploring Corporate Strategy,” 8th ed. (2008)
Based on CMTI’s lack of experience as an international business and the social, economic, and political risks it will face when entering India, this report advises a more cautious approach to market entry in India. As such, CMTI should consider entering the host country via the export entry mode confining the company’s risk exposure to the exportation of the CMTI Smartphone into the country. Additionally, CMTI ought to take a direct approach to exporting its product and acquire a target country agent to help locate host-country buyers, develop transportation arrangements and invest in a robust marketing plan in India.[xxviii]
To be successful in acquiring an Indian business partner, CMTI must employ HUMINT and GEOINT to acquire and subsequently validate an asset/partner in India. This is critically important as the reliability of this asset will be critical to CMTI’s successful penetration of the Indian market. Unreliable sources can lead to catastrophic results.
The recruitment process entails six sequential steps. CMTI must (1) identify an entity in India that can meet its exporting needs, (2) assess the Indian entity’s ability and logistical capacity to provide the adequate and begin the process of determining their motivations and weaknesses, (3) develop a relationship with the Indian entity, (4) form an exporting partnership, (5) regular meeting to discuss corporate culture and goals, (6) once goals are achieved, CMTI can fully enter the market terminate the relationship.[xxix]
To verify whether or not the potential export partner will be useful to CMTI, they can use SIGINT to collect communications emails, phone calls, and other signals from the target to and from the target to ensure their operations are legitimate and they have the resources to help CMTI achieve their goals within India. GEOINT can be used to verify that the potential exporter has a physical location where they claimed and their supply line of communication can be verified and a determination can be made as to the adequacy of their capabilities.[xxx]
Once these have been verified and the expert agent in India has been on-boarded, there must be continual monitoring and validation, because CMTI is relying on the exporter to be an asset on the ground in India, they have to be able to trust and verify the exporter. Through regular interviews, sending an individual to follow the exporter and even polygraphing the exporter, CMTI must maintain a level of control over their asset and limit their exposure to risks from competition or theft of devices. Validation is a critical component particularly as CMTI is following an export entry mode.[xxxi]
4. DEVELOPING A MARKETING PLAN
Developing a marketing strategy in India must be based on an actionable plan that outlines a timeline to achieving CMTI’s goals and objectives. This would include CMTI making decisions on the pricing of the CMTI Smartphone, promotions for the product and logistical considerations.[xxxii] As CMTI is entering the market through direct exporting, it may not have total control over the marketing plan, however, it must remain concerned about the promotion and marketing of the CMTI Smartphone.[xxxiii] A successful marketing strategy must move CMTI’s focus from an American or even global perspective to a localized strategy focused completely on India.[xxxiv] CMTI must become as Indian as any of its indigenous competitors; even as it remains a foreign entrant.[xxxv]
To achieve this, CMTI must implement and execute the four steps of a PSYOP intelligence preparation strategy. These include defining the market environment, analyzing that market, evaluating competitors’ marketing strategies, and determining a course of action.[xxxvi] By implementing this structure, CMTI will be able to determine how to provide what the Indian consumer may want, whilst attempting to bring the costs its product in line with consumer demands.
The only way for CMTI to be effective in defining the market, is for them to know who to target, and through a process called segmentation, CMTI will become deeply knowledgeable about the people in India who are most likely to want to purchase the CMTI. [xxxvii] Deep research; based on groups of potential buyers, grouped together based on similar demographic characteristics (e.g. rural vs. urban, gender, socio-economic situation or lifestyle) will enable CMTI to discover profitable segments of the market for the CMTI Smartphone.
Further, an evaluation of competitor strategies will give CMTI insight into who has already been targeted and formulate an understanding of which demographics may be most open to the introduction of CMTI’s product.[xxxviii] This process will help CMTI understand how to price their smartphone, which region of the country to target and whether to go after urban or rural customers. The following figure illustrates the process:
Figure 3.

Source: Adapted from Root, Franklin R., “Entry Strategies for International Markets” (1994)
Having laid out these factors, CMTI will then be able to define the terms of sale for the CMTI Smartphone. Pricing would then be based on the market factors analyzed and the most successful path historically taken by similar predecessor companies. [xxxix] As a new market entrant to India, and a company committed to reasonable pricing, CMTI has three marketing options a development price strategy, a skimming price strategy and a combination of both.
The development strategy will cause CMTI to lose out in the first few years, however, it will allow them to enter the market and remain consistent as a lower priced provider in the telecommunications industry. In the long-term this will undercut competitors whilst expanding their marketing capacity to undergird large sale volumes and scale up their production of the CMTI Smartphone.[xl]
The skimming price strategy introduces the CMTI Smartphone at a higher price. This strategy looks to gain rapid profits before competitors are able to adequately react with low price alternatives. This will be more feasible for CMTI if they are unable to fund a long-term strategy akin to the development strategy. The profitability associated with this strategy is heavily reliant upon consumers being willing to pay higher prices for the CMTI Smartphone. However this will lead competitors to eventually enter the market with lower priced substitutes, therefore limiting this to a short-term strategy. Given CMTI’s strategy of gradually expanding into India, this strategy seems inappropriate. [xli]
The third option is a combination of both development and skimming strategies. This will see the CMTI Smartphone introduced at a high price in the short-term which will be incrementally lowered as the strategy switches into the long-term phase. The success of this strategy is highly dependent upon on accurately anticipating competitive moves and market conditions. CMTI’s entry strategy makes this a non-optimal choice for the CMTI Smartphone; leaving the long-term development strategy as the most feasible option. [xlii]
Based on research conducted earlier in the paper combined with these principles, CMTI’s marketing strategy ought to be targeted at urban consumers; using the development pricing strategy. Having determined the optimal marketing strategy, CMTI must think protecting itself and the CMTI smartphone for market competitors.
5. INDUSTRIAL / COMMERCIAL SECURITY PLAN
The risk of losing intellectual property (“IP”) is high in India and corruption and bribery are prevalent and enforcement of existing laws in weak. As CMTI expands its operations into India through exporting, whilst physically remaining in the United States, a major priority for the company must be the security and protection of its IP; whether it is trade secrets such as the blueprint for the CMTI Smartphone or the manufacturing process for developing their products. These processes must be protected. It is imperative for CMTI to understand why they may become a target for espionage activity and who would likely conduct these activities against them. CMTI must limit access to sensitive IP to trusted staff. To ensure this an actionable and enterprise-wide training and compliance program must be established. Employees must understand their responsibilities.
Additionally, for CMTI to have an effective counter-espionage posture against competitors in India, they must adhere to the following process: recognize the potential threat, construct a plan to protect that IP, provide continuous training to its employees, develop a plan to handle insider threats, and be proactive about reporting suspicious activity to the authorities.[xliii] To recognize the threat CMTI must understand that they are confronted by a combination of motivations and opportunities by potential spies as the below figure demonstrates.
Figure 4.

Source: Kramer, et. al., “America’s Increased Vulnerability to Insider Espionage” (2007)
By understanding the interplay between the above factors, CMTI will able to construct a robust plan that mitigates against these threats. CMTI must first hire a risk and security executive (“RSE”) to oversee a team that will implement an enterprise-wide security and threat mitigation plan.
As mentioned, this begins with educating employees; which is a crucial element of threat prevention. An informed corporation can lessen their exposure, which is why it is important to understand who is a potential threat and the possible tactics they will use against CMTI. These spies are categorized into two classifications: Outsiders and Insiders. Outsiders tend to be hackers, corporate spies and infiltrators entering the corporation from outside using cyber and physical techniques to access propriety information. Insiders tend to be employees or contractors and the majority of corporate spying crimes are committed by these insiders.[xliv]
The top two techniques that these individuals use are both high-tech and low-tech. Dumpster diving has historically proven to be an effective tool for acquiring IP and it is also a legal method of acquisition once the trash is on a public street. Organizational charts, manuals and contact information can be acquired through these means and can be a treasure trove of information for corporate spies. CMTI must stay aware of its disposal processes and encourage employees to shred all documents ready for disposal.[xlv]
Secondly, hacking and whacking (wireless hacking) are high-tech methods of accessing IP. As global telecommunications capabilities increase, individuals and entities have more capabilities to exploit CMTI’s systems to gain access to valuable information. These individuals may be employees that can exploit their access to gain administrative privileges, or penetrate a system from the outside and intruders infiltrating CTMI’s offices to physically enter their systems. These pose a huge risk to CMTI and can only be mitigated through the protection of the company’s networks and installing guards to verify access and protect the physical location of sensitive information.[xlvi]
As such, to counter an insider and outsider espionage threat CMTI must conduct a thorough initial screening and continuing evaluation akin to the agent acquisition and validation process discussed above in section 3 of this report. Encouraging employees at all levels to identify and report individuals who are exhibiting suspicious behavior which may have CI implications and keep employees feeling enfranchised and engaged to lessen the chance of them being motivated to work against the company.[xlvii] Additionally, cyber and physical security threat mitigation must be centralized under the purview of the RSE, eliminating threat gaps that may occur if these approached are siloed and not integrated into an overall plan.[xlviii]
The RSE must control access to critical information through the encryption and classification of information. CMTI will implement a RED (grave damage/TS)/AMBER (serious damage/S)/GREEN (damage/C) classification[xlix], access to and encryption of information must be followed rigidly to ensure safety. Only known and authorized persons will have access to the information and they must access a wholly internal separate system to access the most sensitive information.[l] In addition to this, internal and external threats must be reported to the authorities such as the FBI, and maintaining strong relations with these entities can help CMTI counter these threats more vigorously. Also, it is important to adhere to basic principles as well. Doors must be locked, sensitive systems and access portals must be locked as well. Portable media devices must be limited or removed at together, cross shred all documents before disposal and limit all access based on internal CMTI security clearance to avoid the vulnerabilities. CMTI’s future profitability is based on how well it can secure and protect its IP and proprietary information.
CONCLUSION
This report took a sequential approach to identifying how CMTI could successfully introduce the CMTI Smartphone to India whilst integrating intelligence techniques. These techniques, if implemented correctly, will allow CMTI to gain the necessary FI to allow their key decision makers to craft an appropriate market entry strategy to compete with domestic and foreign competitors in the Indian telecommunications market. Particularly important to note is that as CMTI is entering the market through the direct export entry mode, continual HUMINT through agent acquisition and asset validation will be crucial to the success of their market entry plan. Intelligence techniques integrated into corporate strategy allow for a more robust and sustainable strategic outlook.
[i]. Root, Franklin R., Entry Strategies for International Markets, New York: Macmillan, 1994, 45 – 46.
[ii]. West, Darrell M., What Consumer Want From Mobile Communications in the United States, United Kingdom, Spain, and Japan, Brookings Institute, 2009.
[iii]. Gannon, John, The Strategic Use of Open-Source Information, Studies in Intelligence 45, no. 3 (2001): 67.
[iv]. Root, Entry Strategies, 1994, p.55
[v]. Arthur S. Hulnick, Fixing the Spy Machine: Preparing American Intelligence for the Twenty-First Century (Westport, CT: Praeger, 1999), 8, 40-41.
[vi]. Epstein, Zach, Global Telecommunications Industry Revenue to Reach $2.1 trillion in 2012, BGR, 2012, Assessed at: http://bgr.com/2012/01/05/global-telecommunications-industry-revenue-to-reach-2-1-trillion-in-2012/, on April 11, 2016
[vii]. Id.
[viii]. “Highlights of Telecom Subscription Data as on 30th June, 2015”, Telecom Regulatory Authority of India, Sept. 2015, Press Release No.47/2015, p.2
[ix]. Id.
[x]. Kiruba, J. and Levi, B., Entry Strategies for Companies in Indian Telecommunications Market, (Doctoral Thesis), 2006, Accessed at: https://doc.rero.ch/record/6023/files/BenjaminLeviKJ.pdf, on April 11, 2016
[xi]. Id.
[xii]. Seitz, Patrick, Managing For Success: Learning to Look Through the Screen, Investor’s Business Daily (2006), Accessed at: www.fuld.com/News/Bus_Daily_8-11-06.pdf, April 12, 2016
[xiii]. Clark, R., Perspectives on Intelligence Collection, Journal of US Intelligence Studies, Vol.20. No.2 (2013), Accessed at: https://www.afio.com/publications/CLARK%20Pages%20from%20AFIO_INTEL_FALLWINTER2013_Vol20_No2.pdf, April 16, 2016
[xiv]. Tyson, Kirk, The Complete Guide to Competitive Intelligence, Merced (Calif.): Leading Edge Publications, 2010, p.3
[xv]. “The Mobile Economy: India 2015” GSMA Intelligence, 2015, p.11, Accessed at: https://gsmaintelligence.com/research/?file=4113a57d43a9e93968e7ed00123ba4b2&download, April 12, 2016
[xvi]. “Samsung Leads India Mobile Phone Market, But Losing Ground to stiff competition: CMR” DNA India, Feb. 8 2015, Accessed at: http://www.dnaindia.com/scitech/report-samsung-leads-india-mobile-phone-market-but-losing-ground-to-stiff-competition-cmr-2059292, April 12, 2016
[xvii]. “India’s Mobile Phone Market” Ipsos Business Consulting, 2014, pp.4 – 5, Accessed at: http://www.ipsosconsulting.com/pdf/Research-Note-India-Mobile-Phone-Market.pdf, April 12, 2016
[xviii]. Id., p.6 – 7
[xix]. Id.
[xx]. “Samsung Leads India Mobile Phone Market”, DNA India, 2015.
[xxi]. Bajarin, Ben, Why India Will Be the World’s Second Biggest Smartphone Market, Time Magazine, Dec. 2, 2014, Accessed at: http://time.com/3611863/india-smartphones/, April 12, 2016
[xxii]. “The Mobile Economy”, GSMA, 2015, p.10
[xxiii]. Tyson, Kirk, “Competitive Intelligence”, 2010
[xxiv]. Ofili, Onyeka Uche, Internationalization: Choosing The Right Entry Mode: Lessons From Ebay’s Strategy In China, European Scientific Journal, 2016, Vol.12, p.209
[xxv]. Root, Entry Strategies, 1994, p.24
[xxvi]. Cavusgil, S. Tamer, et al., Doing Business in Emerging Markets: Entry and Negotiating Strategies, Thousand Oaks (California): Sage Publications, 2002, p.89
[xxvii]. Johnson, G., Scholes, K., & Whittington, R., Exploring Corporate Strategy, 8th ed, Pearson Education Limited, 2008, p.312
[xxviii]. Small Business Administration, Export Business Planner: For Your Small Business, JMH Education Accessed at: www.sba.gov/sites/default/files/SBA Export Business Planner.pdf, April 10, 2016
[xxix]. Burkett, R., An Alternative Framework for Agent Recruitment: From MICE to RASCLS, Studies in Intelligence Vol. 57, No. 1 (Extracts, March 2013), p.13, Accessed at: https://www.cia.gov/library/center-for-the-study-of-intelligence/csi-publications/csi-studies/studies/vol.-57-no.-1-a/vol.-57-no.-1-a-pdfs/Burkett-MICE%20to%20RASCALS.pdf, April 16, 2016
[xxx]. Clark, R., Perspectives on Intelligence Collection, Journal of US Intelligence Studies, Vol.20. No.2 (2013)
[xxxi]. Van Cleave, Michelle K., What is Counterintelligence? A Guide to Thinking and Teaching about CI, Journal of US Intelligence Studies, Vol.20, No.2 (2013), p.58, Accessed at: http://www.afio.com/publications/VAN%20CLEAVE%20Pages%20from%20INTEL_FALLWINTER2013_Vol20_No2.pdf, April 16, 2016
[xxxii].. Root, Entry Strategies, 1994, p.40 – 41
[xxxiii]. Id., 42 – 43
[xxxiv]. Taneja, Girish, et al., Marketing Strategies of Global Brands in Indian Markets, Journal of Arts, Science & Commerce, Vol. 3, Iss.3 (Jul. 2012), Accessed at: http://www.researchersworld.com/vol3/issue3/vol3_issue3_3/Paper_09.pdf, April 12, 2016
[xxxv]. Id.
[xxxvi]. “Psycological Operations Tactics, Techniques, and Procedures”, Department of the Army, Field Manual No. 3-05.301, pp.3-1 – 3-3, Accessed at: https://fas.org/irp/doddir/army/fm3-05-301.pdf, April 12, 2016
[xxxvii]. Helmus, Todd C. et al, Enlisting Madison Avenue: The Marketing Approach to Earning Popular Support in Theatres of Operation, Santa Monica: RAND, 2007, 59-68 Accessed at: http://www.rand.org/pubs/monographs/MG607.html, April 12, 2016
[xxxviii]. Id., pp.59 – 60
[xxxix]. Root, Franklin R., Entry Strategies for International Markets, New York: Macmillan, 1994, p.201
[xl]. Id.
[xli]. Id.
[xlii]. Id.
[xliii]. FBI on Economic Espionage at https://www.fbi.gov/news/stories/2015/july/economic-espionage
[xliv]. Robinson, Shane W., Corporate Espionage 101, SANS Institute 2003 at http://faculty.usfsp.edu/gkearns/Articles_Fraud/corporate%20espionage.pdf
[xlv]. Id.
[xlvi]. Id.
[xlvii]. Kramer, Lisa A. and Richards J. Heuer, Jr., “America’s Increased Vulnerability to Insider Espionage,” International Journal of Intelligence and Counterintelligence, 20, 2007, 50-64 at http://www.pherson.org/wp-content/uploads/2013/06/05.-Americas-Increased-Vulnerability-to-Insider-Espionage-OCR.pdf, Accessed: April 13, 2016
[xlviii]. G4S Corporate Espionage White Paper, “Risk Never Sleeps. 21st Century Threats Corporate Espionage,” at http://www.g4s.us/~/media/Files/USA/PDF-Articles/G4S%20Corporate%20Espionage%20White%20Paper%20web.pdf
[xlix]. Quist, Arvin S., Security Classification of Information, Vol.2 Principles for Classification of Information, 1993, Ch.7 Accessed at: http://www.fas.org/sgp/library/quist2/chap_7.html, April 16, 2016
[l]. Robinson, Corporate Espionage 101, 2003